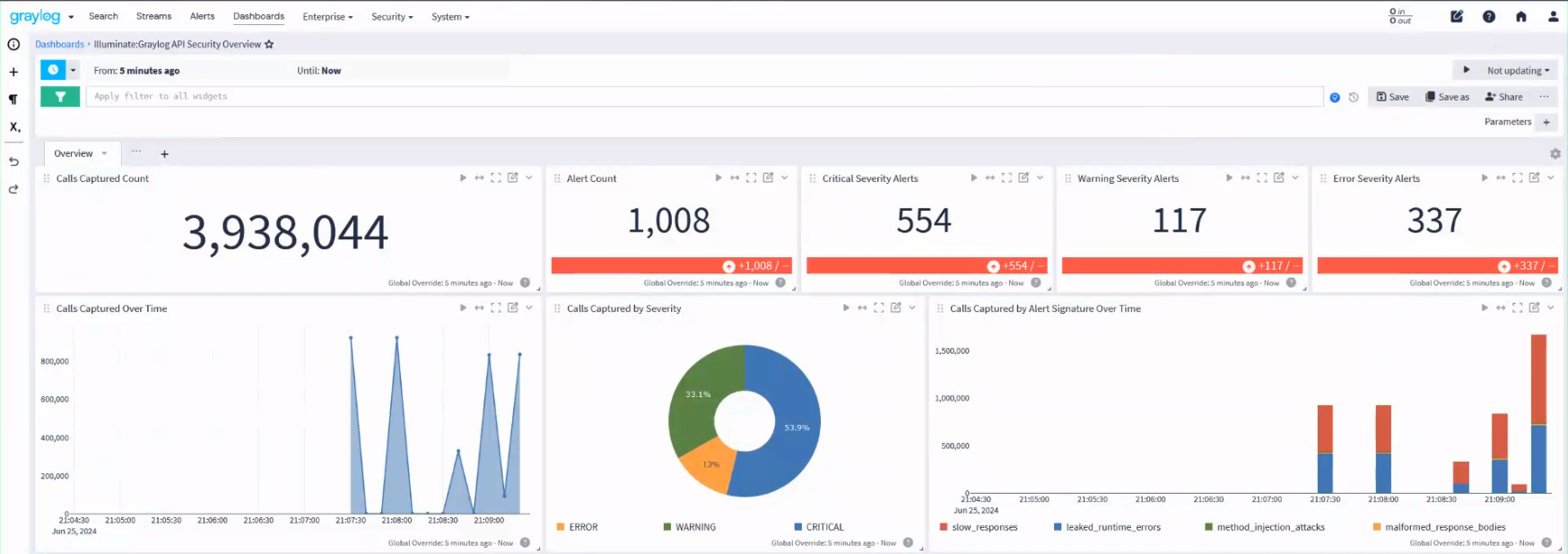
Graylog API Security Content Pack
Graylog API Security captures real API traffic to detect attacks, leaks, and other threats to your APIs. This protection is accomplished with built-in automated and custom signatures and alerts.
Once a signature has reached the threshold for alerting, a corresponding alert message is constructed in GELF format. It is then sent to the previously configured webhook URL destination using HTTP POST requests. See Graylog API Security for more information.
Graylog API Security formats payload strings according to the configured destination for each webhook. Once you have entered the Graylog destination URL for the GELF input, alerts are parsed and displayed in your Graylog API Security dashboard.
Make sure you fulfill the requirements below for a successful integration.
Requirements
-
A Graylog Server with a valid Enterprise license, running Graylog version 6.0 or later.
-
A Graylog Security license to activate the Security product. Contact the Graylog Sales team for more information on purchasing and downloading this license.
-
Install and set up Graylog API Security (see Graylog API Security for details).
-
A GELF HTTP input with the default configuration (see below).
-
Configure alerting in Graylog API Security.
Configure a GELF HTTP Input with the Default Configuration
You can either set up a new GELF HTTP input or configure an existing one with the default configuration:
Bind address: 0.0.0.0
Port: 12201
Enable TLS: False
TCP keepalive: False
Enable Bulk Receiving: False
Enable CORS: True
Configure Alerting in Graylog API Security
-
Navigate to the Settings tab in Graylog API Security.
-
Enter both
localhostand the7700endpoint in the External Network Routing section. -
Enter a URL that points to your Graylog instance in the Default alerting webhook section, for example:
http://mymachine.myorg.net:12201/gelf
Stream Configuration
This content pack includes one stream:
-
"Illuminate:Graylog API Security Messages"
Index Set Configuration
This content pack includes one index set definition:
-
"Graylog API Security Logs"
Log Format
Once a signature has reached the threshold for alerting, a corresponding alert message is constructed with the following fields:
| Field | Type | Description |
|---|---|---|
name
|
string | Name of the signature. |
severity
|
string | Signature severity: NOTICE, WARNING, ERROR, or CRITICAL |
description
|
string | Signature description. |
remediation
|
string |
Signature remediation. Information to help resolve the specific problem. |
current_total
|
integer |
Total number of API calls that match the signature at the time of polling. |
sparkline_totals
|
string |
Unicode characters to represent recent total count history. |
sparkline_alerts
|
string |
Unicode characters to represent recent alert history. |
view_url
|
string |
Graylog API Security URL pointing back to the signature for triage. |
Log Format Example
{"version":"1.1","host":"GraylogAPISecurity","short_message":"Malformed response bodies","full_message":"","_event_source_product":"graylog_api_security","_alert_signature": "malformed_response_bodies","_severity":"CRITICAL","_description":"API calls where the response body cannot be parsed as valid JSON, which is likely to cause client failures, even if the response code is 200 (OK).","_remediation":"Development should fix these specific cases where JSON responses include extra commas, braces, or unescaped characters. These cases are often data-dependent or based on user input that is improperly checked or escaped.","_current_total":79,"_sparkline_alerts":"▁▁▁▁▁▁▁▁▁▁▁▅▅▅▅","_sparkline_totals":"▁▁▁▁▁▁▁▁▁▁▁▃▅▃▇","_view_url":"http://localhost:7700/ui/resurface/search?view=malformed_response_bodies"}
Graylog API Security Spotlight Content Pack
Graylog API Security Spotlight Content Pack offers a dashboard with alerts.