CrowdStrike Falcon is a cloud-native endpoint detection and response (EDR) platform providing AI-powered real-time threat detection, prevention, and response. This technology pack processes CrowdStrike Falcon events, providing normalization and enrichment of detection summaries, EPP/XDR/IDP detections, authentication audit events, firewall matches, remote response sessions, and user activity audit events.
Supported Version(s)
-
CrowdStrike Falcon 7.15.18514.0
Requirements
-
CrowdStrike Falcon 7.15.18514.0 or later.
-
Graylog Enterprise version 6.0.1 or later.
Stream Configuration
This technology pack includes 1 stream:
- "Illuminate:Crowdstrike Falcon Messages"
Index Set Configuration
This technology pack includes 1 index set definition:
- "Crowdstrike Falcon Event Log Messages"
Log Collection
Sending logs via Graylog's CrowdStrike input.
Log Format Example
CrowdStrike Falcon events are delivered in GELF JSON format via the CrowdStrike input.
UserActivityAuditEvent
{"timestamp":1693337449.649,"version":"1.1","host":"customer-id","short_message":"{\"UserId\":\"api-client-id\",\"UserIp\":\"10.1.1.1\",\"OperationName\":\"reveal_token\",\"ServiceName\":\"sensor_update_policy\",\"UTCTimestamp\":1688847014,\"Attributes\":{\"device_id\":\"6614e76223cc47699c09b18e84da6425\",\"message\":\"\",\"seedID\":\"101\"}}","full_message":"{\"metadata\":{\"customerIDString\":\"customer-id\",\"offset\":2802412,\"eventType\":\"UserActivityAuditEvent\",\"eventCreationTime\":1688847014000,\"version\":\"1.0\"},\"event\":{\"UserId\":\"api-client-id\",\"UserIp\":\"10.1.1.1\",\"OperationName\":\"reveal_token\",\"ServiceName\":\"sensor_update_policy\",\"UTCTimestamp\":1688847014,\"Attributes\":{\"device_id\":\"6614e76223cc47699c09b18e84da6425\",\"message\":\"\",\"seedID\":\"101\"}}}","_event_source_product":"crowdstrike_falcon","_vendor_subtype":"UserActivityAuditEvent","_vendor_version":"1.0","_event_created":"2023-07-08T20:10:14.000Z"}
What is Provided
-
Parsing rules for CrowdStrike Falcon events.
-
GIM categorization for detection, authentication, audit, and firewall events.
-
Alert severity with MITRE ATT&CK technique and tactic extraction.
GIM Categorization
GIM categorization is provided for the following event types. All messages sent via the CrowdStrike API will be parsed, but not all event types receive categorization.
| Event Type | gim_event_type_code | gim_event_category | gim_event_subcategory | gim_event_type |
|---|---|---|---|---|
| DetectionSummaryEvent | 301002 | detection | detection.host_detection | hips_detection |
| EppDetectionSummaryEvent | 301002 | detection | detection.host_detection | hips_detection |
| XdrDetectionSummaryEvent | 301002 | detection | detection.host_detection | hips_detection |
| IDPDetectionSummaryEvent | 301002 | detection | detection.host_detection | hips_detection |
| MobileDetectionSummaryEvent | 301002 | detection | detection.host_detection | hips_detection |
| IncidentSummaryEvent | 301002 | detection | detection.host_detection | hips_detection |
| AuthActivityAuditEvent (userAuthenticate) | 100000 | authentication | authentication.logon | logon |
| RemoteResponseSessionStartEvent | 100000 | authentication | authentication.logon | logon |
| RemoteResponseSessionEndEvent | 100000 | authentication | authentication.logon | logon |
| UserActivityAuditEvent | 229999 | audit | audit.default | audit event |
| CSPMSearchStreamingEvent | 229999 | audit | audit.default | audit event |
| CSPMIOAStreamingEvent | 229999 | audit | audit.default | audit event |
| ScheduledReportNotificationEvent | 229999 | audit | audit.default | audit event |
| FirewallMatchEvent | 120000 | network | network.network connection | network connection |
| CustomerIOCEvent | 309999 | detection | detection.default | detection_message |
| HashSpreadingEvent | 309999 | detection | detection.default | detection_message |
| IdentityProtectionEvent | 309999 | detection | detection.default | detection_message |
| ReconNotificationSummaryEvent | 309999 | detection | detection.default | detection_message |
| DataProtectionDetectionSummaryEvent | 309999 | detection | detection.default | detection_message |
CrowdStrike Falcon Spotlight
The CrowdStrike Falcon Spotlight offers dashboards with three tabs: Overview, Authentication, and Detections.
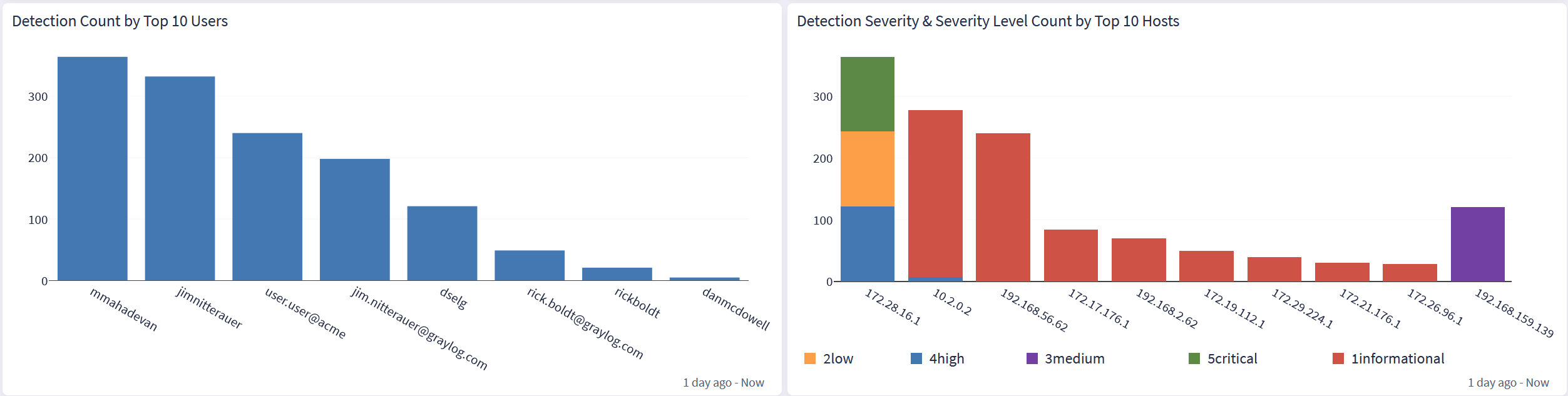
Overview
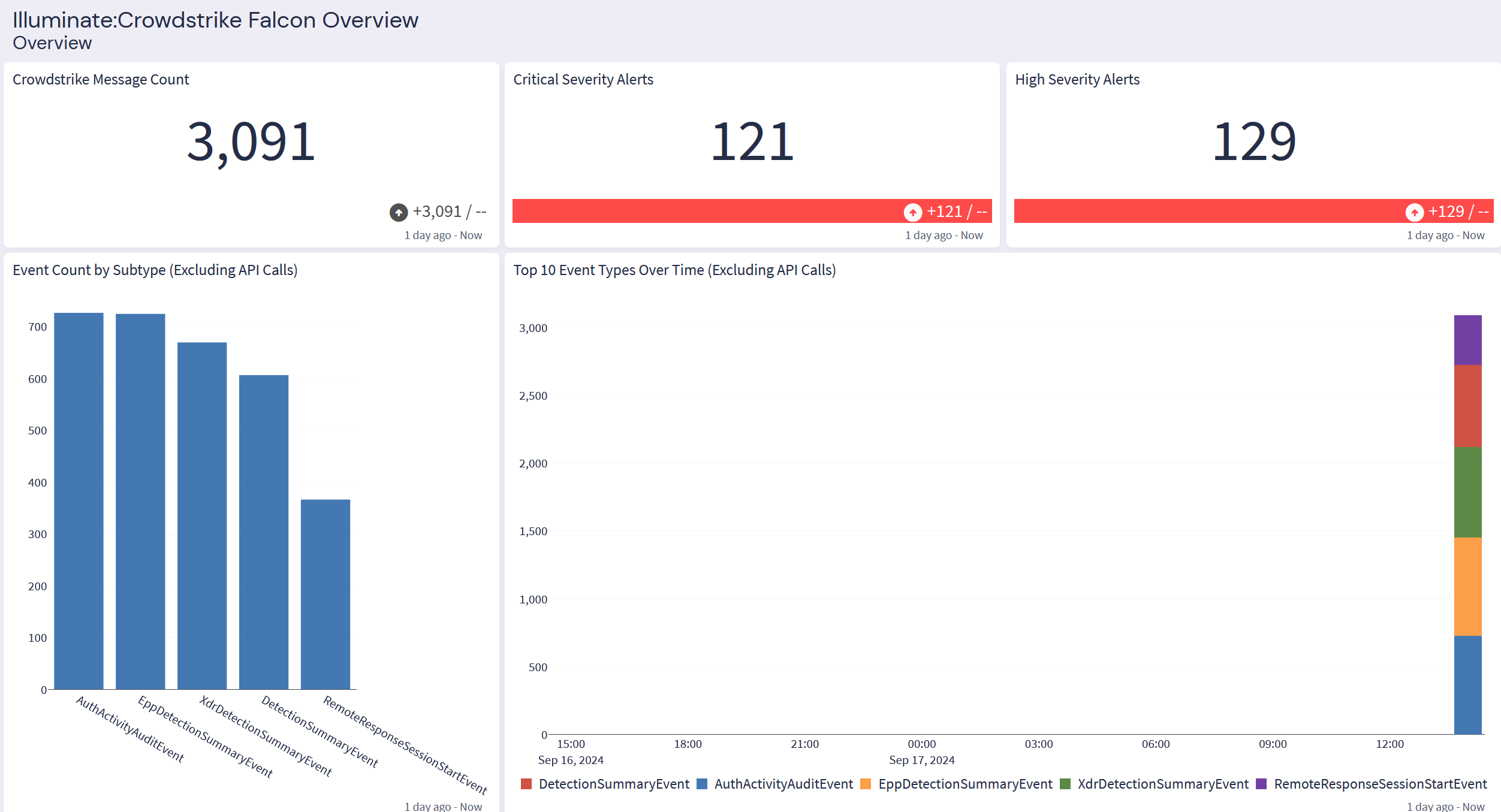
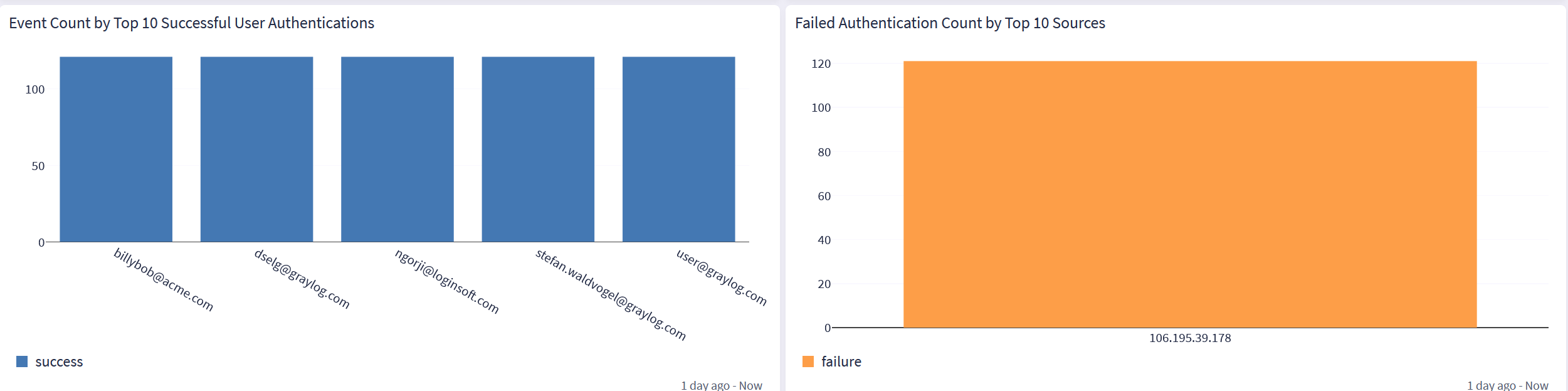
Authentication
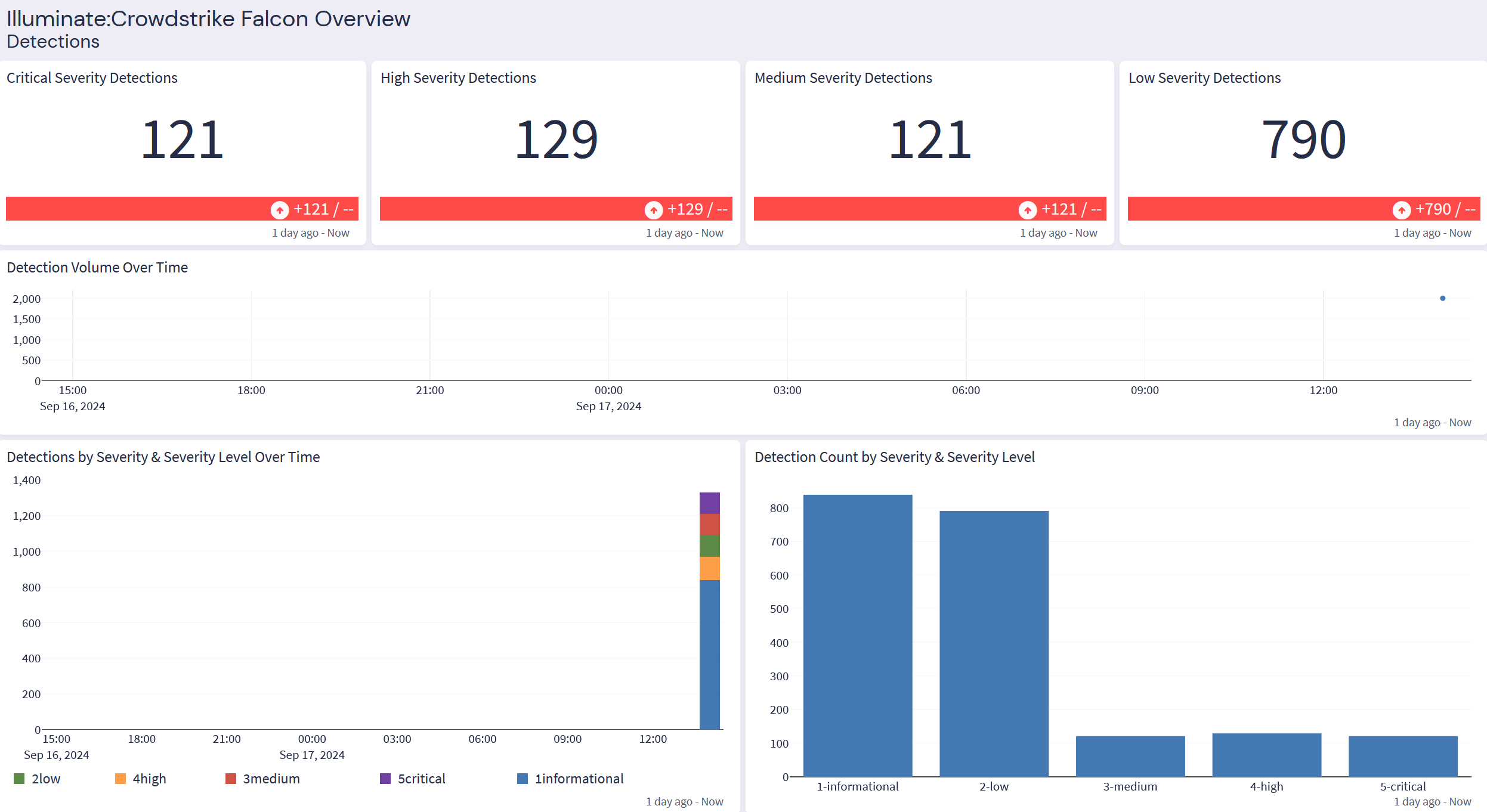
Detections