Apache HTTPD Content Pack
Apache HTTP Server on a Linux system. This pack will parse out and configure Apache2 access logs. It supports two access log formats: Common and Combined logs. And it supports 'normal' logs and virtual hosts logs.
Supported Version(s)
-
Version 2.4
Tested Rsyslog Version
-
8.2212.0
Requirements
-
Graylog 6.1.2+
-
There are two ways to deliver logs that are supported: Filebeat (with Sidecar) and rsyslog.
-
The pack supports a non-standard log folder as long as the name (access.log) does not change.
Stream Configuration
This technology pack includes 1 stream:
- "Illuminate:Apache2 Device Messages"
Index Set Configuration
This technology pack includes 1 index set definition:
- "Illuminate: Apache2 Messages"
Log Format Example
Access
[30/Jan/2023:15:06:52 +0000] "GET / HTTP/1.1" 200 3477 "-" “Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/109.0::1 - Stefan [07/Feb/2023:16:38:37 +0000] "GET /favicon.ico HTTP/1.1" 404 487 "http://localhost/" "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.0.0 Safari/537.36"
Error Logs (beta, we support the following formats)
[Sun Jul 01 01:06:13 2022] [error] [client 1.2.3.4] File does not exist: /var/www/html/robots.txt[Wed Feb 01 00:00:01.584207 2023] [mpm_event:notice] [pid 745:tid 539654844431424] AH00999: Apache/9.4.41 (Ubuntu) configured -- resuming[Wed Jul 15 01:34:12.093005 2020] [proxy:error] [pid 139:tid 133316032] (13)Permission denied: AH00957: HTTP: attempt to connect to 127.0.0.1:9000 (127.0.0.1) failed
Supported SSL Log format (beta support)
[13/Aug/2022:05:41:26 +0600] 192.168.0.100 TLSv1.2 ECDHE-RSA-AES128-GCM-SHA256 "GET /graylog/helper.php?cmd=gethelper HTTP/1.1" 1375
What is Provided
-
Parsing rules to extract Apache logs into Graylog schema-compatible fields. Apache logs get the GIM code “180200” (http.communication).
Field Normalization
Normalize Fields
| Field Name | Description |
|---|---|
| http_referrer | The referrer URL sent by the browser/client (the page that linked to this request), when present. |
| http_request_method | The HTTP method used for the request (for example: GET, POST, PUT), taken from the request line when it matches the expected format. |
| http_request_path | The path (and sometimes query string) requested (for example: /index.html or /api/v1/items?id=1), taken from the request line. |
| http_response_code | The HTTP status code the server returned (for example: 200, 404, 500). |
| http_timestamp | When the request happened, parsed from the timestamp in brackets in the access log. |
| http_user_agent | The client’s User-Agent string (browser/app identifier), when present. |
| http_version | The HTTP version used in the request (for example: 1.1 or 2.0), when included in the request line. |
| ident | Client identity value from the Apache ident field (rarely used). |
| network_bytes | How many bytes were sent back in the response. |
| rawrequest | The full request text as logged, used when it doesn’t match the usual 'METHOD path HTTP/version' format. |
| source_hostname | Client hostname making the request, when the log records a name instead of an IP. |
| source_ip | Client IP address making the request. |
| user_name | Authenticated username for the request (if any). |
Normalize Fields
| Field Name | Description |
|---|---|
| crypto_algorithm | The TLS cipher/cipher-suite recorded for the connection, when present. |
| destination_ip | The target/server IP mentioned in the message, if one is referenced. |
| destination_port | The target/server port mentioned in the message, if one is referenced. |
| event_created | When the error log entry was written (taken from the date/time at the start of the log line, if present). |
| event_error_code | An error code included in the log entry (often Apache-style), useful for grouping similar error types. |
| file_path | A file or path mentioned in the message (for example, a config file path or a request/file path), when present. |
| host_hostname | The hostname referenced in the message when it’s explicitly provided. |
| host_port | The port associated with the referenced host/server, when present. |
| http_host | The host name or IP referenced in the message (often the server/virtual host being evaluated). |
| http_referrer | The referring page URL mentioned in the message, if included. |
| http_uri | The requested URL/URI mentioned in the message (may include path and query string). |
| http_user_agent | A product/version string mentioned in the message as a component identifier (not always a real HTTP User-Agent header in error logs). |
| http_version | The HTTP version referenced (for example, 1.1), when present. |
| network_protocol | The protocol label mentioned in the message (for example, HTTP), if included. |
| process_command_line | The command line Apache logged (common in startup/config messages), captured when the log includes it. |
| process_id | A process ID mentioned inside the message text (if the message explicitly references a PID), which may be different from the logging PID. |
| process_parent_id | The Apache process ID (PID) that wrote this log entry. |
| process_thread_id | The thread ID (TID) that wrote the entry, if Apache is running in a threaded mode. |
| source_ip | The client IP address involved in the event, if the log line includes a client context. |
| source_port | The client’s source port for the request that triggered the message, if included. |
| tls_version | The TLS version used for the connection (for example, TLSv1.2), when present. |
| user_name | The username mentioned in the message (for example, the authenticated user), when present. |
| vendor_apache_error_module | Which Apache component/module reported the message (for example: core, ssl, proxy), when shown in the log line. |
| vendor_attribute | The attribute name mentioned in an authorization message (for example, an LDAP attribute being checked), when present. |
| vendor_auth_path | Where Apache is checking authentication/authorization (for example, an LDAP server address or directory location), when present. |
| vendor_backend_ip | The IP address of the backend server Apache is connecting to (often when acting as a proxy), when present. |
| vendor_child_number | The Apache child/worker number mentioned in the message, if included. |
| vendor_command | A short command/signal name mentioned in the message (for example, a caught or received signal). |
| vendor_error_description | A short error label from within the message (often a brief tag before a colon), when present. |
| vendor_event_action | The main action described by the message (for example: connected, denied, selected, compressed), pulled from the text when possible. |
| vendor_event_description | The main human-readable message text. Some parsing rules may trim it to remove extra prefixes/suffixes so it contains the most useful portion. |
| vendor_event_outcome | A success/failure style word found in the message (for example: failed, accepting, successful), when present. |
| vendor_event_severity | How serious the message is (for example: error, warn, notice, info, debug, trace). |
| vendor_ocsp_header | OCSP response header content shown in the message (for example, a header line like Content-Type: application/ocsp-response), when present. |
| vendor_result | Extra context about an auth/authorization decision (for example, which rule/requirement was evaluated), when present. |
Normalize Fields
| Field Name | Description |
|---|---|
| crypto_algorithm | The TLS cipher suite used for the connection (the encryption method), when logged (for example: ECDHE-RSA-AES128-GCM-SHA256). |
| destination_bytes_sent | How many bytes the server sent back to the client for this request, when present. |
| event_created | When the request was logged, taken from the bracketed timestamp in the log line (if that timestamp is included). |
| http_request_method | The HTTP method used (for example: GET, POST), taken from the request line when it matches the expected format. |
| http_request_path | The requested path (and sometimes query string), taken from the request line (for example: /index.html or /api/v1/items?id=1). |
| http_version | The HTTP version used in the request (for example: 1.1 or 2.0), when included in the request line. |
| rawrequest | The full request text as logged, used when it doesn’t match the usual 'METHOD path HTTP/version' format. |
| source_hostname | Client hostname making the request, when the log records a name instead of an IP. |
| source_ip | Client IP address making the request. |
| tls_version | The TLS version negotiated for the connection (for example: TLSv1.2), when logged. |
Log Collection
Input via Filebeat together with Graylog Sidecar
Please use the official Graylog Sidecar documentation to configure your Graylog server and your client(s).
-
Create an input and an API key and set up Graylog Sidecar.
-
Add your client(s), e.g. web server.
Graylog Server Settings
-
Create a beats input
-
Create a REST API access token
-
Create a (Linux) filebeat configuration under Sidercar > Configuration with a filebeat on linux collector.
-
Configure the file and add:
-
The correct IP (Graylog server IP) under
hosts. -
The log source configured to the desired value and a field
event_source_productwith the valueapache_httpd.Copyfilebeat.inputs:
- input_type: log
paths:
- /var/log/apache2/access.log
- /var/log/apache2/error.log
- /var/log/apache2/httpd-ssl.log
type: filestream
fields_under_root: true
fields:
event_source_product: apache_httpd -
This will only log Apache access logs, but you can add error logs, etc.
-
Finally, save the configuration.
event_source_product and - /var... .
Collection
Configure a Client with Filebeat and Graylog Sidecar
Please refer to the official documentation to set up Graylog Sidecar for Filebeat.
-
Install Sidecar on the remote machine.
Copywget https://packages.graylog2.org/repo/packages/graylog-sidecar-repository_1-5_all.deb
sudo dpkg -i graylog-sidecar-repository_1-5_all.deb
sudo apt-get update && sudo apt-get install graylog-sidecar -
Edit the
/etc/graylog/sidecar/sidecar.ymlfile and configure:-
server_url: GraylogServerIP -
server_api_token: Your API token
Copysudo gedit /etc/graylog/sidecar/sidecar.yml
server_url: "http://192.168.122.52:9000/api/"
server_api_token: "65ol7edseo24mub8o7pu86h2rsr8j9fjjpimtrm9nrpbjso7cnv" -
-
Install, enable, and verify the Sidecar service.
Copysudo graylog-sidecar -service install
sudo systemctl enable graylog-sidecar
sudo systemctl start graylog-sidecar
sudo systemctl status graylog-sidecar -
Install filebeats according to the documentation. Or, here is the download link for the OSS version.
-
If you install it manually, install it again under
/etc/filebeat. -
If you install it via apt-get, then it is in the correct folder.
-
-
Example commands for Ubuntu:
Copysudo gedit /etc/graylog/sidecar/sidecar.yml
server_url: "http://192.168.122.52:9000/api/"
server_api_token: "65ol7edseo24mub8o7pu86h2rsr8j9fjjpimtrm9nrpbjso7cnv" -
Optional. Edit the
filebeat.ymlfile as needed. You do this via the Sidecar configuration in Graylog. -
Start the deamon.
-
If there is a permission issue, you can resolve with:
Copysudo gedit /etc/graylog/sidecar/sidecar.yml
server_url: "http://192.168.122.52:9000/api/"
server_api_token: "65ol7edseo24mub8o7pu86h2rsr8j9fjjpimtrm9nrpbjso7cnv" -
In Graylog, assign a configuration to your machine.
Requirements for Input via Rsyslog
-
A configured UDP (or
TCP_sysloginput on Graylog server). -
Installation of Rsyslog via the official documentation
-
A configured
rsyslog.conf. -
For example
/etc/rsyslog.confwith a UDP input at 1514 on IP 192.168.122.52:Copy# provides UDP syslog reception
$ModLoad imudp
$UDPServerRun 1514
*.* @192.168.122.52:1514;RSYSLOG_SyslogProtocol23Format -
A configured
02-apache2.conf. -
You might need to create the configuration file with:
Copysudo gedit /etc/rsyslog.d/02-apache2.conf -
If it is in the correct folder, Rsyslog will load the file automatically after restarting the Rsyslog service.
-
Example for
02-apache2.confto log access, ssl, and error logs:Copymodule(load="imfile" PollingInterval="10" statefile.directory="/var/spool/rsyslog")
input(type="imfile"
File="/var/log/apache2/access.log"
Tag="apache2_http_access"
Severity="info"
Facility="local6")
input(type="imfile"
File="/var/log/apache2/error.log"
Tag="apache2_http_error"
Severity="info"
Facility="local6")
input(type="imfile"
File="/var/log/apache2/httpd-ssl.log"
Tag="apache2_http_ssl"
Severity="info"
Facility="local6")
local6.access @192.168.122.40:1514 -
Use this command to restart the service on Ubuntu:
Copysudo systemctl restart rsyslog -
You can check the status with:
Copysudo systemctl status rsyslog -
Note that red lines may indicate problems.
Limitations
Error logs are beta; most formats compatible.
Apache HTTPD Content Pack
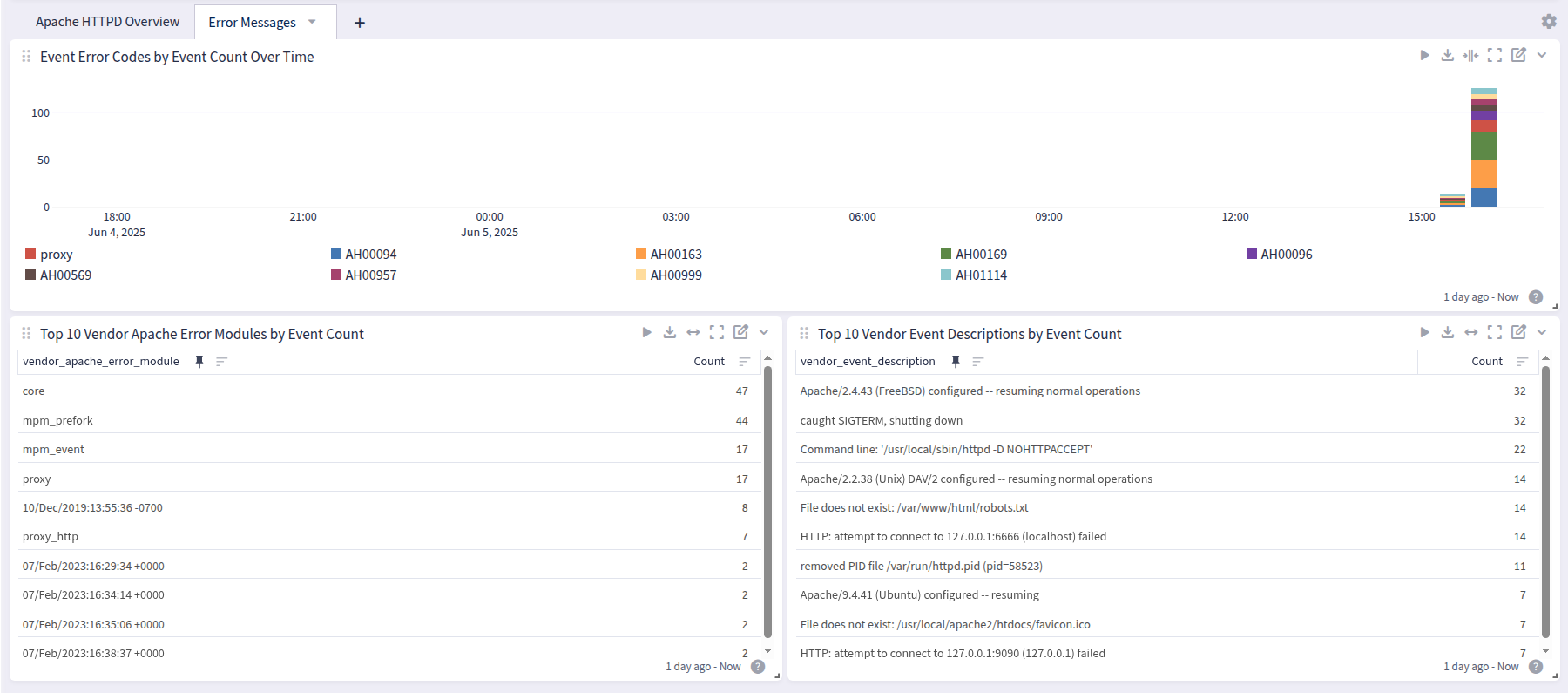
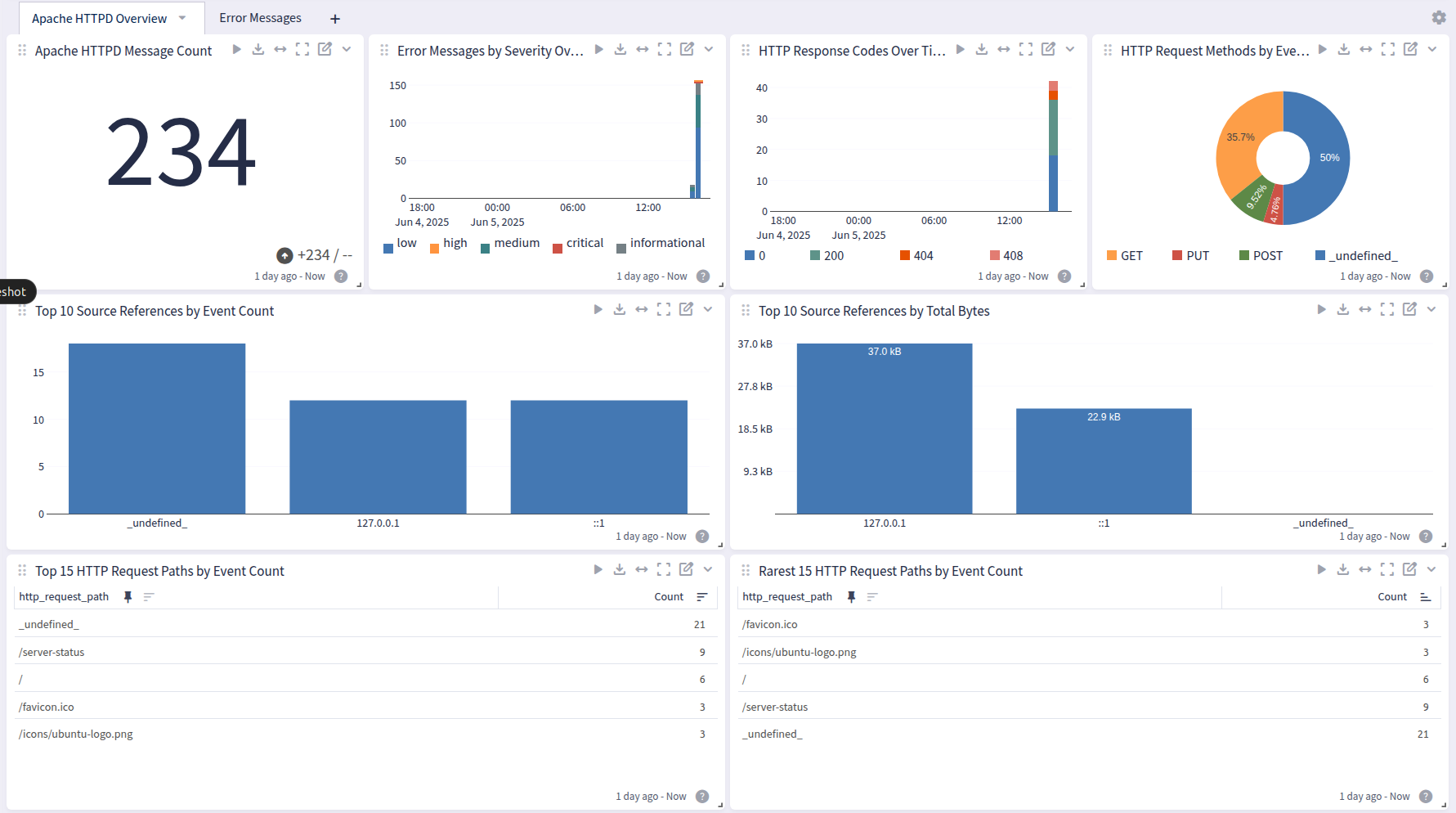
Apache HTTPD offers a dashboard with 2 tabs: Overview and Error Messages:
Overview
Error